Thought Series: Can You Protect What You Cannot See?
Today’s organizations must invest in capabilities, programs, and tools that provide deep visibility into their IT Infrastructure. This is the first step in staying ahead of your enemies.
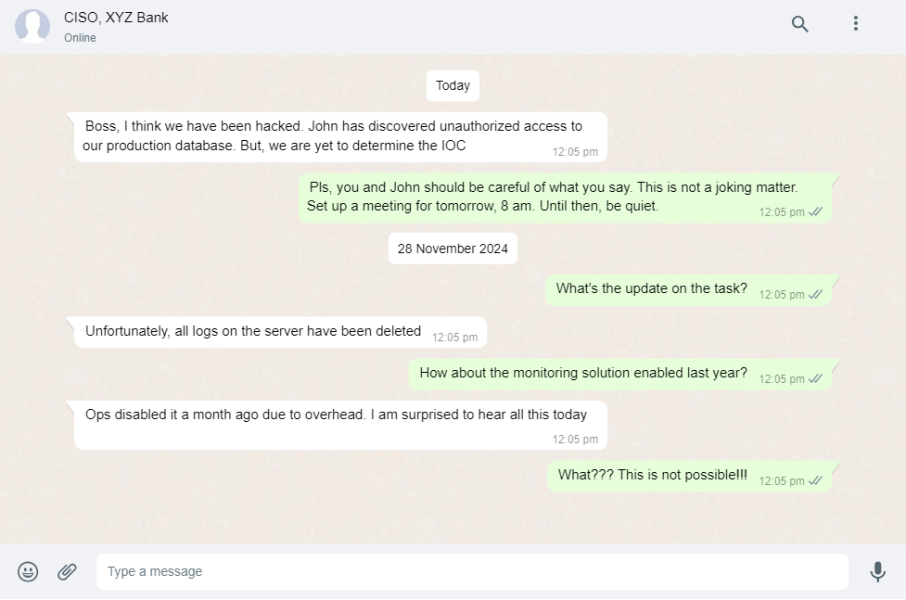
A critical success factor for security teams as they navigate the murky waters of user behavior and anomalies across vastly larger sets of data is Visibility. Visibility in the context of cybersecurity refers to gaining in-depth, real-time insight into all aspects of your organization’s IT environment. It entails seeing and understanding the granular details of network traffic, user behaviors, system configurations and application activity, and more.
According to the NIST Cybersecurity Framework, the first step is to identify - identify key IT assets and classify them based on your organization’s IT risk management strategy. Why is this so critical? The answer lies in the complexity and sophistication of modern cyber threats. Attackers often exploit blind spots in network monitoring, employ lateral movement to infiltrate networks or leverage legitimate service accounts for malicious purposes. It’s in these areas that deep visibility becomes a game-changer.
As organizations continue to navigate the complex landscape of cybersecurity, cultivating deep visibility will remain a central strategy. In the end, the game of cybersecurity is one of vigilance and constant adaptation. With deep visibility as a trusted ally, organizations can meet this challenge head-on, bolstering their defense and securing their digital frontier.
Please remember this: The clearer your view, the stronger your defense. Cybersecurity visibility doesn’t just illuminate the way forward—it actively paves the path toward more robust cybersecurity, empowering organizations to navigate the digital world with confidence and resilience.
Lastly, Visibility is an important step—but it’s only the first step. Once you have an accurate picture—in real-time—of the servers, applications, services, and data on your network, you also need a security platform that can scale and keep up to provide a streamlined understanding of your security posture, along with the information and context you need to prioritize and address any issues that are identified.